Chrome Extension For Web Scraping
- DataMiner Scraper is a data extraction tool that lets you scrape any HTML web page. You can extract tables and lists from any page and upload them to Google Sheets or Microsoft Excel. With Scraper you can export web pages into XLS, CSV, XLSX or TSV files (.xls.csv.xlsx.tsv) You can use Dataminer Scraper for FREE in our starter subscription plan.
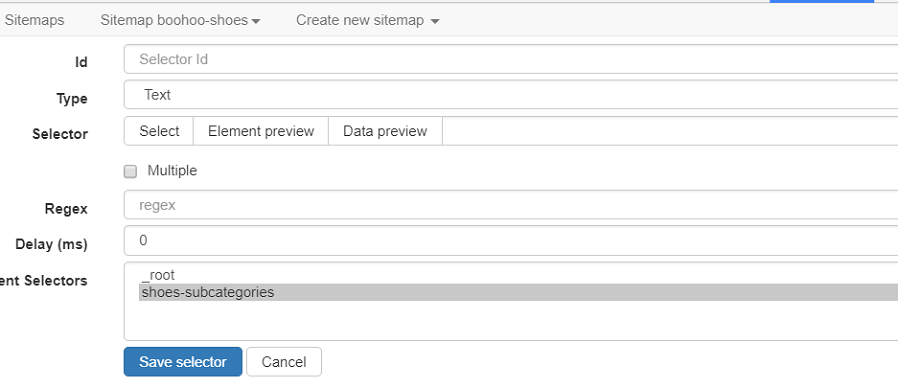
- How to use Web Scraper? There are only a couple of steps you will need to learn in order to master web scraping: 1. Install Web Scraper and open Web Scraper tab in developer tools (which has to be placed at the bottom of the screen for Web Scraper to be visible); 2. Create a new sitemap; 3. Add data extraction selectors to the sitemap; 4.
- The most popular web scraping extension. Start scraping in minutes. Scrape sites and export data in CSV format directly from your browser. Use Web Scraper Cloud to export data in CSV, XLSX and JSON formats, access it via API, webhooks or get it exported via Dropbox. Start using Web Scraper now! Install Web Scraper. Chrome extension Firefox.
You can Buy Me a Coffee Now: this video, you will learn how to extract multiple web pages by using google chorme. 6- If Web Scraping with Google Chrome Extensions on Oddsportal website is not possible, then what free scrapping tools to use and details of your instructions to scrape it. Skills: Web Scraping, Excel, Data Entry, C Programming. See more: google chrome doesn show website graphics.
Facebook has taken legal action against the makers of malicious Chrome extensions used for scraping user-profiles and other information from Facebook's website and from users' systems without authorization.
The two defendants developed and distributed the malicious browser extensions through the Chrome Web Store working under the 'Oink and Stuff' business name.
'They misled users into installing the extensions with a privacy policy that claimed they did not collect any personal information,' Jessica Romero, Director of Platform Enforcement and Litigation, said.
'Four of their extensions — Web for Instagram plus DM, Blue Messenger, Emoji keyboard, and Green Messenger — were malicious and contained hidden computer code that functioned like spyware.'
The four extensions are still available for download in Google's Chrome Web Store and they currently have more than 54,000 users.
Facebook systems' not compromised
After being installed on the users' computers, these Chrome extensions also installed malicious code in the background which allowed the defendants to scrape user data from Facebook's site.
The malicious Chrome add-ons were also used to surreptitiously collect data unrelated to Facebook from the users' web browsers.

While the users were browsing the Facebook website, the extensions automatically scraped account information including the victims' name, user ID, gender, relationship status, and age group among others.
Chrome Extension For Web Scraping And Burning
Romero added that the defendants did not compromise Facebook's security systems during their malicious activity but, instead, they only used the extensions installed on users' devices to scrape data.
'We are seeking a permanent injunction against defendants and demanding that they delete all Facebook data in their possession,' Romero concluded.
'This case is the result of our ongoing international efforts to detect and enforce against those who scrape Facebook users’ data, including those who use browser extensions to compromise people’s browsers.'
Legal action against platform abuse
This action is part of a long series of instances where Facebook took legal action against entities attempting to abuse the company's platform and services.
For instance, in March 2020, Facebook sued domain name registrar Namecheap and its proxy service Whoisguard 'for registering domain names that aim to deceive people by pretending to be affiliated with Facebook apps' and often being used 'for phishing, fraud and scams.'
Instant Data Scraper For Chrome
In October 2019, Facebook filed another lawsuit against domain name registrar OnlineNIC and its privacy service ID Shield for allowing the registration of lookalike domains such as facebook-mails.com and www-facebook-login.com.

The same month, Facebook also sued Israeli cyber-surveillance firm NSO Group and its parent company Q Cyber Technologies for creating and selling a WhatsApp zero-day exploit.

The exploit was used in May 2019 to exploit the platform's video calling system to deploy malware as part of an attack targeting over 100 high-profile targets including journalists, human rights defenders, and government officials.
Related Articles:
